Looking for Calvin and Hobbes
Monday, December 5, 2022When I started working at my first job after completing the college, one of the perks was getting uninterrupted access to the internet and email. 20 years ago internet access at home was not very common in India. We often visited ‘internet cafes’ to eletronically connect to the world by paying 10 Rs/hr.
The ‘free’ supply of internet connectivity opened world of enterntainment opportunities for us. We used email to share jokes, and memes.
One day I received a cartoon in my Inbox where a big tiger and mischievous looking kid were making some philosophical comment about life. I hadn’t seen these cartoon characters before. Growing up I either read cartoons in Marathi newspapers or in the Marathi comics books. This cartoon was very different than what I was used to. I loved that cartoon and found its name.
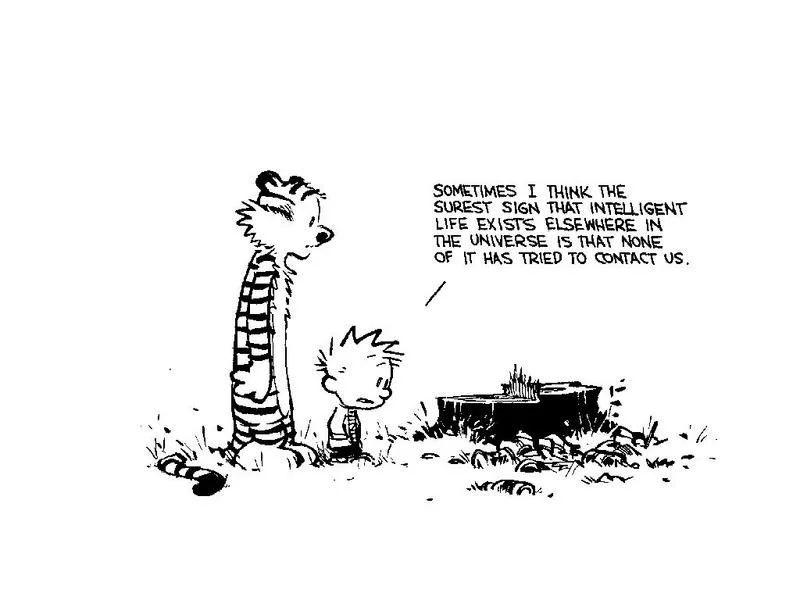
Calvin and Hobbes turned out to become one of my favorite cartoons ever.
Over the next few months I hunted for these cartoons all over internet. And at one point of time I had almost 3000+ cartoons from most of the strips downloaded on my computer. But what I found surprising was how little we knew of it’s creator Bill Watterson.
I recently finished listening to an audiobook about Bill Watterson. Bill Watterson is media-shy. Other than his famous commencement speech and some information on Wikipedia, its difficult to learn more about this talented cartoonist. Nevin Martell’s Looking for Calvin and Hobbes is a wonderful, entertaning and informative book about Bill Watterson’s creativity, and philosophy towards work and life.
Martell interviews Watterson’s friends, ex colleagues from syndicate, peers and whoever was influenced by the talented cartoonist for this book. The book uncovers Watterson’s early years as a struggling cartoonist as well as his journey to become one of the most influential cartoonists. It brings forward Watterson’s views on syndication, commercialization and licensing of art. It discusses Watterson’s creative process and also his own inspirations. I enjoyed reading the book and highly recommend it to other Calvin and Hobbes fans.